Overview
Safehats is a Bug bounty platform that offers several benefits to organizations looking to enhance their cybersecurity posture and identify vulnerabilities in their software and systems.
Here are some of the key advantages of using Safehats Platform :
- Continuous Security Testing
- Access to a Global Talent Pool
- Rapid Identification of Vulnerabilities
- Cost-Effective Security Testing
- Real-World Testing
- Bug Bounty Community Engagement
Safehats also provides comprehensive Role-Based Access Control (RBAC)l to ensure that various stakeholders, including security researchers, program owners, and platform administrators, have appropriate levels of access and control within the platform.
-
Security Researcher: Role for individual or group who reports vulnerabilities, submit reports, viewing own reports, collaborate with other reports, Communicating with Program owner.
-
Program Owner (Enterprise): Enterprise or Administrator Role manages their bug bounty programs. Permissions include creating and editing programs, setting bounties, reviewing and accepting reports, and communicating with researchers and Administrators. Provide Granular access to other user for any kind of operation.
-
Platform Administrator (SMO): Administrators manage the overall platform. Their permissions include managing user accounts, reviewing reports, resolving disputes, and handling payments.
High Level Architecture
The Safehats Web Based Platform is designed for high availability, incorporating robust load balancing capabilities in both active-active and active-passive modes to ensure continuous service and optimal performance. Additionally, the application can be configured in a DC-DR (Data Center-Disaster Recovery) architecture, enhancing its resilience and reliability in various operational scenarios. The Safehats platform is highly scalable, able to adjust dynamically to meet changing demands. It supports automatic load balancing, which helps in efficiently distributing traffic and resources across servers, thereby maximizing uptime and minimizing response times. This makes the Safehats platform an ideal solution for organizations seeking a dependable and flexible web-based security platform.
High-Level Architecture Component
1.User Interface (UI):
- Web-based portal accessible from various devices, providing users with access to the platform's features.
2.Load Balancers:
- Active-Active Load Balancers: Multiple load balancers working simultaneously to distribute incoming traffic evenly across all available servers, ensuring optimal performance and availability.
- Active-Passive Load Balancers: A standby load balancer is available to take over in case the primary load balancer fails, enhancing reliability.
3.Web Servers:
- Clusters of web servers configured in both active-active and active-passive modes to handle requests. These servers process and respond to user actions on the UI.
4.Application Servers:
- Servers that handle the business logic of the platform, processing data, performing operations, and serving dynamic content based on user requests.
5.Data Center (Primary Site) and Disaster Recovery (DR) Site:
- Primary Data Center: Hosts the operational environment where the data is actively managed and used.
- Disaster Recovery Site: An alternative facility that can be switched to in case the primary site fails, ensuring continuity of operations.
6.Database Servers:
- High availability database clusters that store and manage critical application data. Configured for replication between the primary data center and the DR site to ensure data integrity and availability.
7.Storage Systems:
- Scalable storage solutions that support the data needs of the application, configured for automatic data replication and backup between the primary and DR sites.
8.Network Infrastructure:
- Robust internal and external networking setups that connect all components with high-speed links, ensuring reliable and secure data transfers.
9.Security Layers:
- Comprehensive security measures including firewalls, intrusion detection systems (IDS), and encrypted data transmissions to protect against unauthorized access and data breaches.
Flow
- User Interaction: Users access the platform through the web UI, with requests managed by load balancers that distribute the load across web and application servers.
- Processing and Data Management: Requests are processed by application servers, with data stored in high availability databases. Continuous data replication is maintained between the primary and DR sites.
- Failover Mechanisms: In case of a server or component failure, the system automatically redirects traffic and operations to standby systems or the DR site without user intervention.
- Scalability and Load Balancing: The system dynamically adjusts resources and balances the load across servers to handle varying demand levels efficiently.
Key Features
SafeHats is a leading platform in the cybersecurity industry, offering robust and comprehensive features tailored to meet the demands of enterprise clients. The platform is ISO certified and recognized by leading analysts, including Gartner and Forrester, enhancing its credibility and trust in the market. SafeHats is fully compliant with GDPR, ensuring the protection and privacy of user data across international markets. It supports a global audience of researchers, with international KYC processes in place, and boasts a network of over 5,000 security researchers. The platform is designed to cater to modern security challenges, offering extensive support for IoT and API testing, ensuring that all aspects of an organization’s digital footprint are secure. Integration capabilities are a key strength of SafeHats, allowing seamless connections with ticketing tools, SIEM systems, and other security tools, enabling organizations to manage vulnerabilities effectively within their existing workflows. The platform also offers flexible customization options, including branding and personalized email communications, allowing organizations to tailor the user experience. With a focus on enterprise clients, SafeHats provides exceptional support and multi-language capabilities, ensuring that it meets the diverse needs of a global user base.
1.Types of Programs:
The SafeHats platform offers a variety of security programs tailored to meet the diverse needs of organizations:
- Vulnerability Disclosure Program (VDP)
- Bug Bounty Program
- Private Bug Bounty Program
- Vulnerability Assessment and Penetration
- Managed Programs
- Security Research Grants
- Customized and Tailor Made
2.Web-Based Platform with High Availability:
- The platform is designed to be web-based, ensuring that it is accessible from anywhere with an internet connection. High availability guarantees that the platform is operational 24/7, minimizing downtime and ensuring reliability for users across the globe.
3.Scalability:
- Built to handle a high volume of traffic, the platform supports thousands of concurrent users without performance degradation. This scalability is crucial for handling large-scale programs and multiple simultaneous submissions from security researchers.
4.Security:
- The platform implements stringent security measures to protect user data and ensure the confidentiality, integrity, and availability of the system. This includes encryption of all data at rest and in transit, regular security audits by a CERT-In empaneled agency, and maintaining a valid audit clearance certificate.
5.Single Sign-On (SSO) Support:
- Integrates with popular identity providers to offer seamless and secure user authentication. SSO support simplifies access for users, reducing the need for multiple login credentials.
6.Role-Based Access Control (RBAC):
- Provides a comprehensive permission system that assigns specific roles to users, such as administrators, security researchers, and program managers. This ensures that users only have access to the data and functionalities relevant to their role.
7.API Support:
- Offers a well-documented, RESTful API that enables integration with external tools and services, allowing for automation and extended functionality of the platform.
8.Vulnerability Reporting:
- Enables researchers to submit detailed vulnerability reports, including steps to reproduce, screenshots, and proof-of-concept code. This feature is critical for providing actionable insights to program managers.
9.Vulnerability Triage:
- A system for program managers to review, prioritize, and validate vulnerability submissions. This ensures that critical issues are addressed promptly while less severe vulnerabilities are appropriately managed.
10.Bug Tracking:
- Includes robust bug tracking and management features, such as labeling, filtering, and search capabilities, to help organizations manage reported vulnerabilities efficiently.
11.Collaboration Tools:
- Facilitates collaboration among security researchers by enabling them to work together on vulnerability reports and share findings, fostering a community-driven approach to security.
12.Reputation and Leaderboard System:
- Implements a reputation system that ranks security researchers based on the quality and quantity of their submissions, encouraging healthy competition and rewarding top contributors.
13.Reward Management:
- Provides tools for the distribution of monetary rewards, points, or swag for valid vulnerability submissions, making it easier to manage compensation for security researchers.
14.Customizable Program Policies:
- Allows organizations to create and manage their own bug bounty policies and guidelines, ensuring that the program aligns with their specific security requirements and objectives.
15.Program Templates:
- Offers pre-built templates for various types of bug bounty programs, such as web application, mobile app, and IoT testing, enabling organizations to quickly launch effective security programs.
16.Asset Management:
- A system for managing in-scope assets, such as domains, IP addresses, and application instances, ensuring that all relevant targets are covered by the bug bounty program.
17.Integration with Existing Tools:
- Supports integration with popular vulnerability scanners, ticketing systems, and Security Information and Event Management (SIEM) platforms, enhancing the platform's capability to work within existing security ecosystems.
18.Reporting and Analytics:
- Provides comprehensive reporting and analytics features to track program performance, identify trends, and make data-driven decisions to improve security.
19.Data Export:
- Allows users to export vulnerability data in standard formats, such as CSV, JSON, or XML, facilitating data analysis and reporting outside the platform.
20.Notification System:
- Sends customizable email or SMS notifications for new submissions, updates, and other platform events, ensuring that users are always informed about critical activities.
21.Mobile App Support:
- Offers a mobile app for iOS and Android devices, enabling researchers and program managers to access the platform on-the-go, increasing flexibility and responsiveness.
22.Multi-Language Support:
- Provides a platform that supports multiple languages, making it accessible to a global user base and enhancing inclusivity.
23.Custom Branding:
- Allows organizations to customize the look and feel of their bug bounty program with their own logo, colors, and domain, ensuring consistency with their brand identity..
24.Automated Vulnerability Detection:
- Includes automated scanning tools to identify common security vulnerabilities, complementing manual efforts by security researchers.
25.Customizable Access Controls:
- Allows organizations to define granular access controls based on user roles and permissions, ensuring that sensitive information is only accessible to authorized individuals.
26.Live Chat with Bug Bounty Hunters:
- Supports live chat functionality, enabling real-time communication between program managers and security researchers, facilitating quick resolution of queries and collaboration.
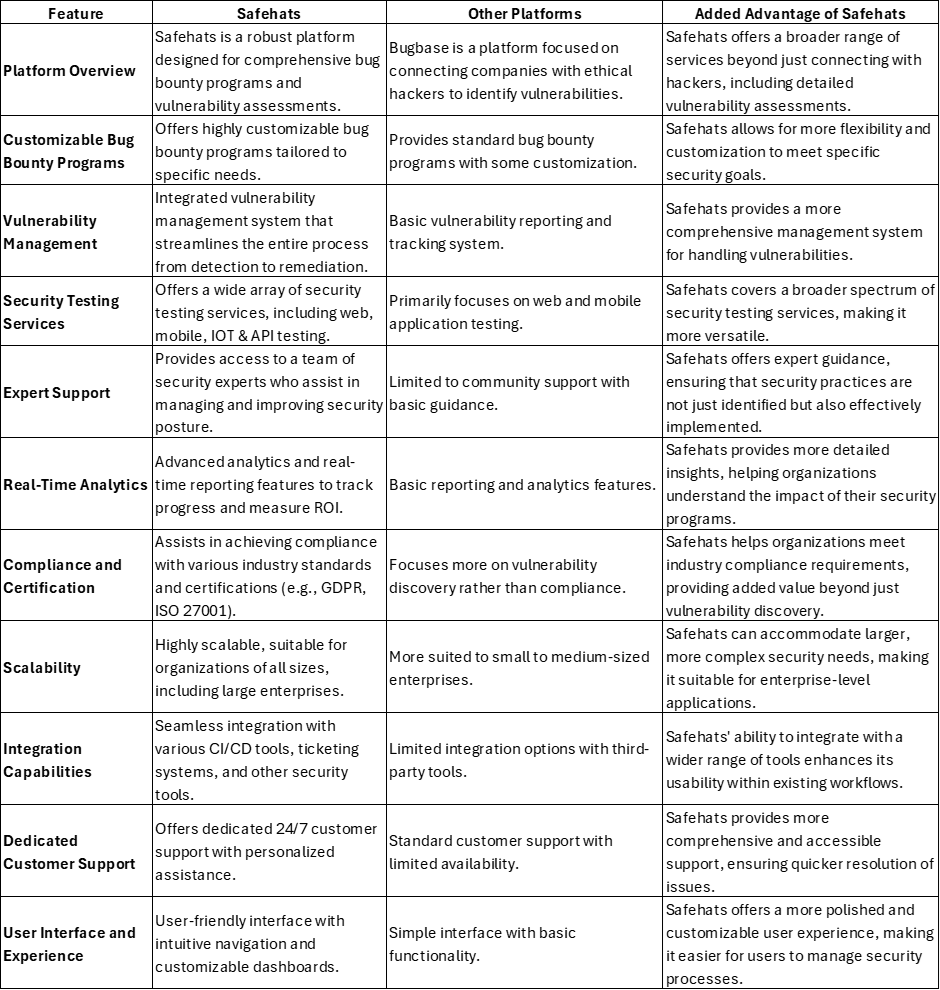
Platform Comparison